Ios 26.4.2 Security: 3 reasons Apple’s tiny fix turned into a major privacy test
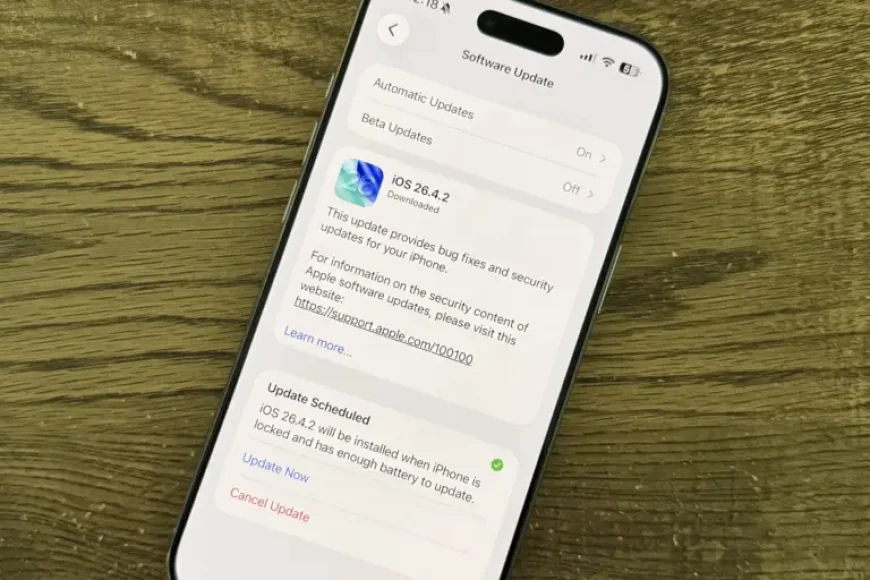
The iOS 26. 4. 2 security update looked routine at first glance: one patch, one notification bug, one small release. But the timing gave it outsized importance. The flaw involved notifications marked for deletion that could be unexpectedly retained on the device, and that detail matters because it created a path for deleted Signal messages to remain accessible. For users who rely on private messaging, ios 26. 4. 2 security is no longer just a software note; it is a reminder that privacy can hinge on what a phone keeps behind the scenes.
Why this iOS 26. 4. 2 security fix matters now
Apple said the update addresses a single issue in Notification Services. On its face, that is a narrow repair. In practice, the vulnerability became significant because it affected content tied to deleted notifications rather than a visible app interface. That means the problem sat inside the device’s own storage behavior, not in how a message was typed or sent. The update also arrived with a broader message for users: if you use Signal, install it as soon as possible and restart the iPhone. The headline here is not just that Apple patched a bug. It is that the patch suggests a gap between user expectations and device retention rules.
Deleted messages, notification storage, and the hidden risk
The key concern is what was preserved after deletion. The context shows that deleted Signal content was retrieved from copies saved in the device’s push notification database. That is a different kind of privacy failure than a stolen password or a hacked account. It points to a system-level behavior where fragments of communication can survive even after the app itself is removed. In other words, ios 26. 4. 2 security is about more than a fix for one app; it is about how operating systems handle the lifecycle of sensitive content. For messaging apps that emphasize end-to-end encryption, automatic deletion, and on-device history storage, the security promise can still be weakened if notifications remain available in internal memory.
What the FBI use of the flaw reveals
The context indicates the vulnerability was used by the FBI in a Texas case linked to an attack on the Prairieland ICE detention center facility. That detail raised the stakes because it showed the flaw was not theoretical. It was used to extract Signal messages from a defendant’s iPhone even after Signal had been deleted. The broader implication is that device forensics can still reach beyond the app itself when notification data lingers. That is why ios 26. 4. 2 security has drawn unusual attention: the patch closes a technical opening, but it also exposes how much weight can sit inside a single notification record. For users, the lesson is simple and unsettling: deletion does not always mean disappearance.
Expert reaction and the privacy debate
Signal president Meredith Whittaker said the platform asked Apple to address the bug and stressed that notifications for deleted messages should not remain in any operating system notification database. Signal said it was very happy Apple fixed the issue and called the matter one that touches the fundamental human right to private communication. The Electronic Frontier Foundation said Apple’s fix addressed only part of the issue. Thorin Klosowski, a security and privacy activist at the Electronic Frontier Foundation, added that push notifications are typically routed through Apple or Google servers before reaching phones, and that the content may be visible to those companies along with metadata about what apps send notifications and when. That makes ios 26. 4. 2 security part of a larger privacy debate, not a standalone patch.
Regional and global impact for secure messaging users
The immediate impact reaches Signal users, but the wider effect is global. Journalists, government officials, and others who depend on secure messaging are now confronted with a reminder that privacy can be undermined at the notification layer even when a service is built around encryption. The context also shows Apple issued the update just to fix this vulnerability, which suggests the company viewed the flaw as serious enough to stand on its own. For device makers, messaging platforms, and privacy advocates, that raises a larger question about where responsibility ends. If notifications can outlive deleted apps, then every secure communication system must treat the operating system itself as part of the threat surface. That is why ios 26. 4. 2 security matters beyond one phone or one trial.
Apple has closed the flaw, but the episode leaves a larger question hanging: if deleted messages can survive inside notification storage, what else on a phone remains after users believe it is gone?