Google Reveals Hackers Leveraging AI as a Powerful Weapon
Recent developments in cybersecurity are raising alarms as hackers are increasingly leveraging artificial intelligence (AI) for malicious purposes. The Google Threat Intelligence Group (GTIG) recently highlighted how various AI tools, including Google’s Gemini, are being exploited to conduct cybercrimes, such as password and bank information theft.
AI as a Tool for Cybercrime
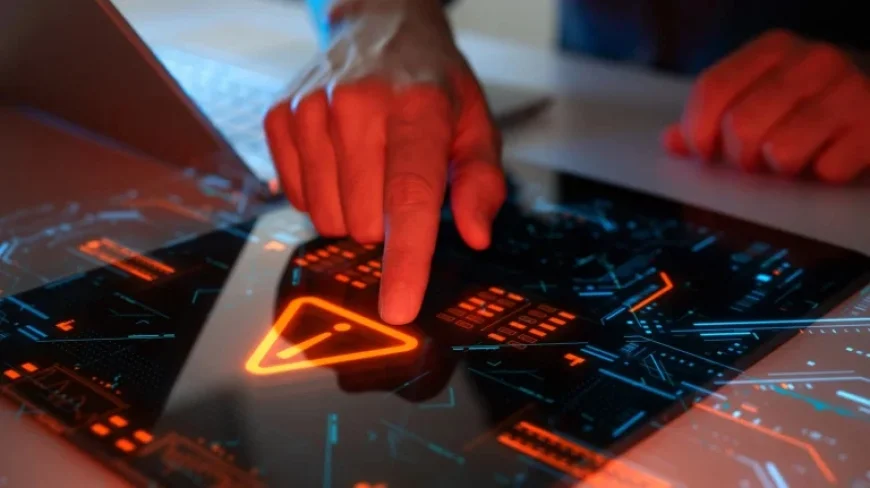
AI technology can automate numerous tasks and enhance productivity. However, malicious actors have found ways to manipulate its capabilities to their advantage. According to GTIG, AI is being utilized for various illicit activities, including:
- Intellectual property theft
- Surveillance
- Development of new malware
In response to these threats, Google took measures to mitigate these abuses but underscored the potential impact of these acts on future cybersecurity developments.
Target Profiling and Phishing Scams
One of the alarming uses of AI is its ability to quickly scan the internet for information. Hackers can utilize AI to compile lists of potential victims and enhance their phishing strategies. For instance:
- The hacker group known as “UNC6418” employed Gemini to target members within Ukraine’s defense sector.
- Another hacker, “UNC2970,” connected to North Korea, masqueraded as a recruiter targeting cybersecurity professionals.
AI can produce phishing emails that appear genuine, effectively building trust with victims during interactions. This advancement complicates the traditional ability to identify fraudulent communications.
Creation of Malware
The coding capabilities of AI are being exploited by hackers to create sophisticated malware. For example, AI software can be manipulated to perform complex tasks autonomously. One case study involves the hacker “UNC795,” who managed to get Gemini to generate AI-integrated code auditing features. While the implications of this attempt remain uncertain, it reflects a growing interest in complex, self-functioning malware.
Emerging Threats
GTIG has presented several proofs of concept showcasing novel malware capabilities. One notable example is a malware variant named HONESTCUE. This tool operates as a backdoor Trojan, utilizing Gemini to download additional malicious codes discreetly. Despite being developed by amateur coders, this raises serious concerns about what skilled hackers could achieve with similar resources.
Conclusion
The rise of AI in cybercrime is a pressing issue. As hackers increasingly exploit these technologies, the cybersecurity landscape faces evolving challenges. Organizations must stay vigilant and enhance their defenses against this new era of digital threats.