Poland Faces Surge in Cyberattacks, Energy Sector Hit by Destructive Assault

poland experienced 2 1/2 times more cyberattacks in 2025 than the year before, totaling 270, 000 incidents, Deputy Minister of Digital Affairs Paweł Olszewski said on March 24, 2026 at 12: 10 PM ET. The attacks included a destructive infiltration of the country’s energy system in December that Polish authorities called unprecedented among NATO and European Union members and suspected to have originated in Russia. Coordinated strikes on the morning and afternoon of Dec. 29 hit a combined heat and power plant supplying heat to almost 500, 000 customers and multiple wind and solar farms, though the electricity supply was not disrupted.
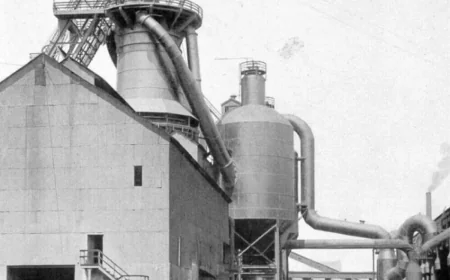
Poland’s energy sector hit
The December intrusion is the standout incident in a year of sharply rising malicious activity. During the morning and afternoon of Dec. 29, coordinated cyberattacks struck a combined heat and power plant that supplies heat to almost 500, 000 customers and targeted multiple wind and solar farms. Authorities described the intrusion as destructive rather than financially motivated, and CERT Polska issued a detailed public report in late January on the technical aspects while asking the cyber community for input.
Marcin Dudek, head of CERT Polska, said, “The attack was a significant escalation. ” Dudek added that Poland had seen mostly ransomware incidents in the past, where financial motives were primary, and that the December case showed a motivation of destruction. He said he was not aware of any previous destructive cyberattack on the energy sector among NATO or EU countries and warned that had larger energy units been targeted the stability of poland’s energy grid could have been substantially impacted.
Government response and threats identified
Deputy Minister Paweł Olszewski said the scale of incidents is rising significantly year after year and summarized the totals: 270, 000 cyberattacks in the last year. The government, led by Prime Minister Donald Tusk, has beefed up cyber defenses since the start of Russia’s full-scale invasion of Ukraine on Feb. 24, 2022, in response to what it views as a growing threat from Russia.
Polish authorities suspected the December attacks were the work of a single “threat actor, ” and CERT Polska’s analysis of internet infrastructure used in the incident — including domains and IP addresses — found those online resources had been used previously by a Russian threat actor known as “Dragonfly, ” also called “Static Tundra” or “Berserk Bear. ” Dudek noted that while Dragonfly has targeted the energy sector before, the December incident appears to be a destructive escalation not seen previously from that actor in energy systems.
Polish secret services have not publicly identified an alleged culprit; CERT Polska’s remit allows it to describe modus operandi and point to likely threat actors while investigations continue.
What’s next
CERT Polska has invited input from the wider cyber community and continues technical analysis of the December incident; investigators and security teams remain focused on tracing infrastructure and assessing future risk. The government’s strengthened defenses since early 2022 will remain a central part of the official response as officials monitor incident counts that rose 2 1/2 times in 2025. With public technical reporting completed and secret services continuing their work, the immediate focus is containment, analysis and hardening of systems to prevent repeat destructive intrusions in poland.