Urgent National Security Agency alert: Reboot your internet router immediately

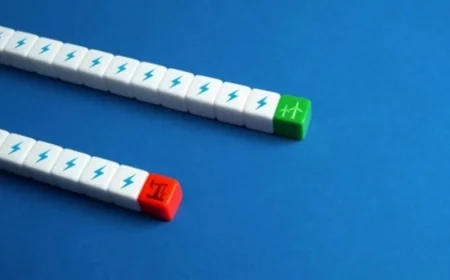
national security agency guidance is now part of a fast-moving federal warning after U. S. authorities disrupted a Russian intelligence hacking network tied to compromised home and small-office routers. The warning centers on vulnerable SOHO devices and lands as officials push users to check router settings, firmware, and DNS configurations right away. The message is direct: a reboot can help with some threats, but it will not solve this one.
What federal authorities say happened
Last week, the FBI and the Justice Department said they carried out a court-authorized operation to neutralize a U. S. portion of a network of small office and home office routers compromised by a unit within Russia’s Main Intelligence Directorate, known as GRU Military Unit 26165. The routers were used to support malicious Domain Name System hijacking against worldwide targets of intelligence interest to the Russian government, including people in the military, government, and critical infrastructure sectors.
the attackers used known vulnerabilities to steal credentials for thousands of TP-Link routers and then altered router settings to send requests to GRU-controlled servers. In court documents, the government said it tested the operation extensively on the affected firmware and hardware and found that, aside from blocking GRU access, it did not interfere with normal router function or collect legitimate users’ content information. national security agency advice was released alongside FBI guidance as part of the broader defensive response.
national security agency guidance for users
Brett Leatherman, assistant director of the FBI’s Cyber Division, said Russian GRU cyber actors had compromised vulnerable routers in the U. S. and around the world and were using them to conduct espionage. He said unsuspecting Americans in at least 23 states owned routers that were exploited, and he pointed to the scale of the threat as the reason for the court-authorized disruption.
Leatherman said the FBI, the NSA, and international partners from 15 countries released a public service announcement with technical information and defensive guidance. He said rebooting a router may reduce some threats, but it will not address this one. The recommended steps include replacing end-of-life and end-of-support routers, upgrading to the latest available firmware, verifying the authenticity of DNS resolvers listed in router settings, and reviewing firewall settings to prevent unwanted exposure of remote access.
Why the warning matters now
The federal response reflects a wider concern about router exploitation, especially when older devices remain in service long after support ends. One of the models named in the federal announcement is the TP-Link TL-WR841N, a Wi-Fi 4 router originally released in 2007, and the targeted list includes multiple TP-Link models.
Daniel Dos Santos, vice president of research at the cybersecurity company Forescout, said there is a big trend of exploiting routers, both consumer and enterprise. A Microsoft Threat Intelligence report on the attack said DNS hijacking gives nation-state actors persistent, passive visibility and reconnaissance at scale. Microsoft identified more than 200 organizations and 5, 000 consumer devices impacted by the campaign.
What users should do next
For people who rely on older routers, the immediate priority is checking whether the device is still supported and whether its firmware is current. If the router is on the affected list or has reached end-of-service status, officials say replacing it is the safer move. TP-Link Systems said the affected models reached end-of-service and end-of-life status several years ago, and it has developed security updates for select legacy models where technically feasible.
The bottom line is that the national security agency guidance is not meant to create panic, but to force action before attackers can keep using exposed routers as quiet entry points. More defensive steps may follow as agencies and international partners continue to track the impact of the operation and the wider threat to home networks.