Nemoclaw Signals a New Security Inflection Point as Enterprises Test Agent Strategies

nemoclaw arrives as a one-command stack that installs Nemotron models and the OpenShell runtime for the OpenClaw agent platform, adding privacy and security controls meant to make autonomous AI agents more trustworthy and accessible.
What Happens When Nemoclaw Is Deployed in the Enterprise?
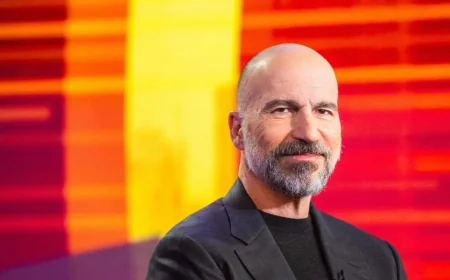
NVIDIA announced a NemoClaw stack for the OpenClaw agent platform that installs NVIDIA Nemotron models and the newly announced OpenShell runtime in a single command and layers in privacy and security controls for self-evolving, autonomous AI agents, or claws. Jensen Huang, founder and CEO of NVIDIA, framed OpenClaw as an operating system for personal AI and positioned NemoClaw to bring guardrails and scalability to that open framework. Peter Steinberger, creator of OpenClaw, said the broader ecosystem is building claws and guardrails to let anyone create secure AI assistants.
NemoClaw uses the NVIDIA Agent Toolkit to optimize OpenClaw, and it installs OpenShell to provide open models and an isolated sandbox that adds data privacy and security to autonomous agents. The stack aims to provide the infrastructure layer beneath claws that gives them the access they need while enforcing policy-based security, network and privacy guardrails.
What If OpenClaw Strategy Meets Enterprise Guardrails?
Key features described in the announcement sketch how enterprises might adopt agentic systems while addressing governance concerns:
- Single-command deployment: NemoClaw installs models and runtime components together to simplify onboarding.
- Isolated sandboxing: OpenShell creates an isolated runtime intended to protect data and enforce policies for always-on agents.
- Local + cloud model mix: Agents can run open models like Nemotron locally on dedicated systems or use frontier models in the cloud a privacy router.
- Hardware flexibility: NemoClaw can run on dedicated PCs, workstations and AI supercomputers to support continuous agent operation.
- Enterprise readiness posture: The platform is framed as enterprise-grade with security and privacy features integrated from the start.
The move also echoes broader industry signals that governance platforms for AI agents are becoming crucial infrastructure; a Gartner report highlighted governance platforms for agents as essential for enterprise adoption. NVIDIA describes NemoClaw as an early-stage alpha release and positions it as the starting point for building toward production-ready sandbox orchestration while acknowledging rough edges in early developer builds.
Scenario mapping based strictly on the announcement and related signals yields three trajectories: best-case — enterprises rapidly adopt NemoClaw-like stacks to run controlled, productive agents that combine local models with cloud resources under policy guardrails; most likely — mixed deployments where pilots reveal integration and orchestration work remains and organizations iterate on sandboxing and connectivity patterns; most-challenging — fragmentation and immature sandbox orchestration slow enterprise rollouts while security gaps require additional tooling and governance layers.
Who wins and who loses under these trajectories is straightforward from the release: organizations that standardize on secure agent stacks and invest in local compute and orchestration win by gaining controlled productivity; creators of open agents and models win if they interoperate with the stack; organizations that skip strategy or treat agents as experimental risk lose ground on control and compliance.
For readers planning next steps, treat the NemoClaw announcement as both an opportunity and a blueprint. Evaluate pilot use cases that pair local Nemotron instances with cloud models through privacy routers, prioritize sandbox orchestration and policy enforcement, and expect iterative improvements as the effort moves from alpha toward production. Keep governance and integration work at the center of deployment planning and test always-on agent behaviors on dedicated hardware before scaling.
Uncertainty remains: the platform is presented as early-stage, orchestration tooling is being built out, and enterprises will need to validate sandboxing and data flows in their own environments. Close attention to the stack’s security controls, local/cloud balance and sandbox orchestration will determine whether organizations capture the promised benefits of agents. Plan pilots, monitor guardrail effectiveness, and iterate — nemoclaw