Code leak Reveals Mythos Contradiction: Most Powerful Model and Exposed Internal Tooling

The leaked code and unpublished drafts tied to Anthropic upend the company’s public rollout: internal material shows a model called Claude Mythos described as “by far the most powerful AI model we’ve ever developed, ” while more than 512, 000 lines of exposed code reveal unreleased features and operational lapses that leave the firm vulnerable.
What did the Code leak show?
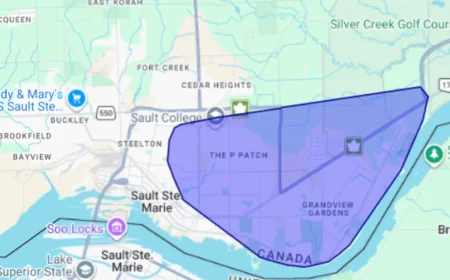
Verified facts: The release packaging for a recent Claude Code update included a source map file that exposed a TypeScript codebase. The exposed material runs to more than 512, 000 lines and contains references to unreleased features, internal instructions for Claude, and notes on the system’s memory architecture. The leaked assets also contain an unpublished draft blog post and related documents: Anthropic acknowledged that a “human error” in the configuration of its content management system allowed those drafts to be publicly searchable, and the company removed public access after being informed of the data exposure. Alexandre Pauwels, cybersecurity researcher at the University of Cambridge, assessed the unsecured cache and identified close to 3, 000 assets linked to the company’s blog that had not been published. Roy Paz, senior AI security researcher at LayerX Security, also reviewed material from the unsecured data store.
Among the unreleased code artifacts are descriptions of a UX element described as a Tamagotchi-style pet that “sits beside your input box and reacts to your coding, ” and a feature labelled “KAIROS” that appears designed to function as an always-on background agent. The codebase includes developer comments, including a candid note that “memoization here increases complexity by a lot, and im not sure it really improves performance. ” The draft blog post in the cache names a new model tier called Capybara, positioned above the company’s existing Opus line, and describes the specific model variant Claude Mythos as complete and under testing with early access customers. Anthropic described the new model in the draft as “a step change” in performance and “the most capable we’ve built to date. “
Who is responsible and what must change?
Verified facts: Anthropic identified the incident as a packaging and configuration error, and Christopher Nulty, Anthropic spokesperson, stated that no sensitive customer data or credentials were exposed; he described the issue as a release packaging problem caused by human error and said the company is implementing measures to prevent recurrence. Arun Chandrasekaran, AI analyst at Gartner, assessed the situation as posing risks, citing the possibility that exposed internal code could enable actors to attempt to bypass guardrails, while also describing the episode as a prompt for Anthropic to strengthen operational maturity.
Analysis: Taken together, the technical exposure and the simultaneous appearance of an unpublished draft about a new flagship model create a contradiction between product ambition and operational control. The draft positions Claude Mythos (and the Capybara tier) as a leap in capability; the exposed code reveals detailed product internals and unfinished features, including agentic behavior that would change how systems act on behalf of users. When a company’s most advanced work appears in the same accidental public cache as raw developer notes and source maps, two risks converge: proprietary technical detail becomes available for study, and internal risk assessments intended to be private are visible before mitigations are finalized. That combination elevates cybersecurity and policy concerns beyond a routine packaging error.
What is verified is limited to the artifacts in the cache, the company’s public remediation steps, and assessments by named researchers and analysts. What remains uncertain without further disclosure is the full scope of internal controls that failed, the timeline for testing and deployment of Mythos, and whether additional exposed assets exist beyond the identified cache. Those uncertainties are material to customers and regulators evaluating operational risk.
Accountability demand: Anthropic’s dual admission—that it is training and testing a model described in the drafts as exceptionally capable and that a configuration error left extensive code and unpublished content exposed—creates an urgent need for transparent remedial steps. The company should publish a detailed incident report, verified by independent reviewers, that inventories exposed assets, confirms the absence or presence of customer data, and specifies process and tooling changes to prevent similar packaging errors. External review by named security researchers and institutional auditors would address the gaps highlighted by Alexandre Pauwels, Roy Paz, Christopher Nulty, and Arun Chandrasekaran and help restore confidence in handling of pre-release model materials and developer code. The leaked code and draft announcements together demand that Anthropic pair its technical ambitions for Mythos with tightened operational rigor and public accountability.