Axios Npm: Supply Chain Compromise Strikes Package with 100M Weekly Downloads
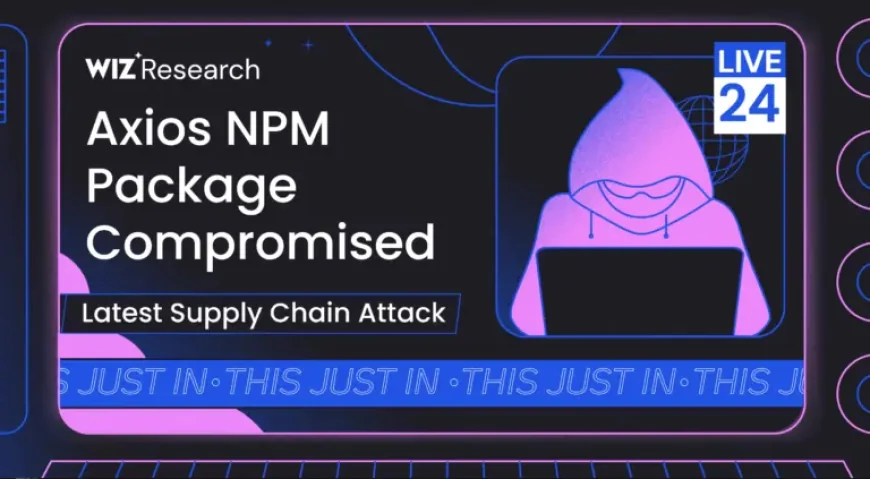
A high-impact supply chain attack has compromised the axios npm distribution used across development and cloud environments, creating a rapid propagation path to deliver remote access trojans. The axios npm package, downloaded over 100 million times per week, was altered through a compromised maintainer account to pull in a malicious dependency that executes platform-specific RAT payloads during installation.
Background & context: how the compromise unfolded
Security researchers identified a staged compromise that abused an axios maintainer account on the npm registry. The attacker first published a benign-looking dependency, then followed with a trojanized update that introduced a new package named plain-crypto-js. That follow-up release contained an installer dropper that fetches platform-specific second-stage payloads and executes them on Windows, Linux and macOS systems.
The breadth of exposure is tied to axios’s prevalence: the package is present in a large share of cloud and code environments and is downloaded about 100 million times per week. A security vendor observed the malicious plain-crypto-js package being created and later detected the malicious update through automated systems; another vendor noted the attacker had staged the operation over many hours to evade detection by establishing an initial publishing history.
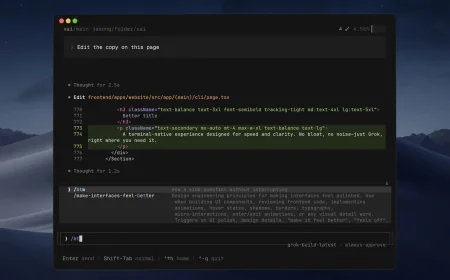
Axios Npm: deep analysis, technical impact and immediate indicators
The malicious installer component behaves as a dropper that retrieves and executes operating-system–specific payloads from a command-and-control host. Once executed, the second-stage payloads perform reconnaissance and beaconing, presenting comprehensive RAT capabilities including remote shell execution, process listing and directory browsing in addition to persistence techniques. Observed artifacts and indicators include outbound connections to sfrclak. com and the Internet Protocol address 142. 11. 206. 73, and dropped files named /Library/Caches/com. apple. act. mond on macOS, %PROGRAMDATA%wt. exe on Windows, and /tmp/ld. py on Linux.
Two malicious axios releases were identified as tainted and removed: versions that introduced the plain-crypto-js dependency. At least one advisory that assessed the incident observed measurable execution in a subset of affected environments; one estimate found that execution occurred in about 3% of exposed environments during the short exposure window. Given that some malicious activity occurs at install time, build pipelines and developer workstations are high-priority areas for audits.
Expert perspectives and response guidance
Open Source Malware called the compromise historically significant: “This will go down in history as one of the most successful software supply chain attacks ever, ” the community threat database stated. Step Security and another automated detector flagged the active compromise and the staged publishing technique used to evade automated scans.
Axios primary maintainer Jason Saayman’s npm account was taken over and the registered account email changed before the attacker published the poisoned packages manually through the npm command-line interface, bypassing the project’s normal continuous integration pipeline. Security advisories and vendor guidance emphasize immediate audit and containment actions: pin projects to unaffected tags such as axios@1. 14. 0 or axios@0. 30. 3, search networks for outbound connections to the identified C2 host and IP, and scan endpoints for the listed dropped files and persistence artifacts.
Additional recommended steps include removing malicious artifacts from endpoints and build systems, rotating credentials if execution is suspected, and investigating developer machines and CI systems for signs of unauthorized access or persistence. The malicious dependency used obfuscation and anti-analysis strategies, and its multi-platform design underscores the need for cross-platform detection and mitigation.
Regional and global impact: ripple effects for development and cloud ecosystems
The incident illustrates how a single widely used package can act as an amplifier across diverse environments. Because axios is embedded in a large percentage of cloud and code stacks, even a brief availability window for malicious releases produced detectable execution across organizations. The risk spans local developer workstations, CI/CD pipelines and production workloads, and the supply chain nature of the compromise raises the possibility of downstream contamination in dependent projects.
Governance and risk teams should prioritize inventorying where the package is used, whether the tainted versions were downloaded or executed, and whether any secrets or credentials may have been exposed during the malicious activity. The multi-platform nature of the payloads means that incident response playbooks must coordinate Windows, macOS and Linux remediation steps concurrently.
As organizations triage exposure, recommended indicators of compromise include the plain-crypto-js package presence, the axios versions that pulled it in, outbound connections to sfrclak. com or 142. 11. 206. 73, and the platform-specific dropped files. Pinning to known-good axios tags and scanning build artifacts and caches are immediate containment measures.
Will developer tooling and registry practices change fast enough to blunt this class of supply chain attacks, or will the ease of publishing and the scale of package reuse continue to produce high-impact compromises?