Anthropic leaks part of Claude Code’s internal source code and Mythos testing — the human and business fallout

At dawn, a misconfigured content cache left draft material and internal files exposed from anthropic, turning private development notes and a large source map into a public problem that security researchers and engineers raced to contain.
Anthropic leak: what was exposed and who noticed
The exposure included an unpublished draft blog post describing a new, more powerful model called Claude Mythos and references to a new model tier named Capybara. The draft described Mythos as “by far the most powerful AI model we’ve ever developed” and said Capybara would be larger and more capable than the company’s previous top-tier models. Early access trials of the new model were noted in the draft.
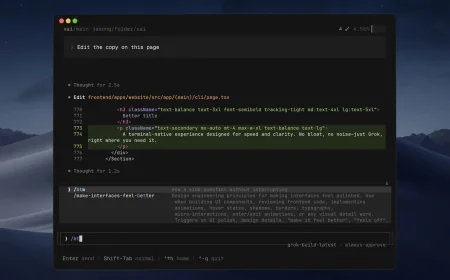
Separately, a large JavaScript source map file tied to the company’s agent product was unintentionally included in a public package release. The map measured roughly 59. 8 MB and, when expanded, reflected a codebase of roughly half a million lines of TypeScript. The file enabled mirrors of the internal code to appear on public code hosting sites within hours of discovery. A member of the developer community, Chaofan Shou, an intern at Solayer Labs, broadcasted the discovery on social media at 4: 23 am ET, which accelerated public scrutiny.
How specialists and researchers framed the risk
Alexandre Pauwels, a cybersecurity researcher at the University of Cambridge, and Roy Paz, a senior AI security researcher at LayerX Security, reviewed the exposed cache. Pauwels noted that close to 3, 000 previously unpublished assets linked to the company’s blog were accessible in the data store. The researchers described the material as draft content and internal artifacts left in an unsecured, publicly searchable data lake.
Security practitioners examining the leaked source map highlighted architectural details that could be consequential for competitors and attackers alike. The exposed code revealed design patterns around long-running agent memory, a three-layer memory architecture, and feature flags named in ways that suggest always-on autonomous agent behavior. Developers who analyzed the material described a “self-healing memory” approach and a strict write discipline designed to prevent context pollution during long sessions.
Business and human consequences: revenue, trust, and the scramble to fix mistakes
The leak arrived at a sensitive commercial moment. Internal figures shown in the exposed materials placed the company’s annualized revenue run-rate near $19 billion, with the agent product contributing an annualized recurring revenue around $2. 5 billion and enterprise customers representing approximately 80% of that revenue. Those numbers, visible in internal artifacts, underscore why the exposure of proprietary design and product plans is both an intellectual-property and a competitive risk.
For engineers and product teams, the immediate human response was damage control: removing public search access to the cache, auditing release packaging, and tightening configuration controls. The company described the root cause as a human error in content management configuration and characterized the exposed drafts as unpublished materials. Internal teams are rolling out measures intended to prevent a recurrence.
For the security researchers who found and reviewed the material, the episode was a reminder of how a single misconfiguration can turn routine development artifacts into a strategic disclosure. For rank-and-file engineers, the public mirror of an expansive codebase meant confronting hours of reverse engineering and external commentary about internal design choices.
What happens next: containment, reassessment, and unanswered questions
In the hours after the exposure was discovered, access to the data store was restricted and the company confirmed that a release packaging issue had included internal source code in a public package. The organization emphasized that no customer credentials or sensitive customer data were exposed, and that measures would be implemented to reduce the chance of repetition.
Beyond immediate containment, the leak forces two practical responses: a technical clean-up to remove or rotate any exposed build artifacts and a strategic reassessment of what development artifacts are permitted in searchable caches. It also invites a longer conversation inside engineering organizations about how to balance developer convenience against the risk of leaving sensitive design or commercial information discoverable.
Back where the story began — the quiet server room and the overlooked content-management toggle — the draft blog and the large source map now read differently. What had been routine internal work became a public lesson in operational hygiene, with reputational and competitive stakes attached. As teams patch configurations and scrub repositories, one lingering question remains: how will the company rebuild confidence among customers and partners after internal plans and code briefly passed through the public eye?
The broken cache that revealed Mythos, Capybara notes, and large sections of Claude Code is closed now, but the episode will follow engineers and executives for months as anthropic assesses both technical fallout and trust repair in the marketplace.