Github Takedowns and 500,000 Lines: Twin Incidents Shake the AI Industry

The AI sector is reeling after two linked security events this week: a supply-chain attack that exposed customer data at a model-training firm and a human-error leak that released 500, 000 lines of Anthropic source code. Anthropic has filed multiple copyright takedown requests to remove the leaked material from github, but the release of detailed implementation notes and prompting techniques has already amplified concerns about long-term vulnerability and misuse.
What happened and why it matters now
The incidents began when a supply-chain compromise tied to an open-source project cascaded into the exposure of a training-services provider’s customer data. That provider works with a range of labs and training specialists and counts major AI developers among its clients. Separately, Anthropic disclosed that a large tranche of its own source code was made public through human error; the company emphasized the leak was not the result of an external hack. While the leaked materials did not include the datasets that directly power Anthropic’s Claude agent, they did contain details on how the company can be prompted to perform particular tasks—material that can change the threat profile for downstream misuse.
Github takedowns and the permanence problem
Anthropic has pursued copyright takedown requests to have the leaked files removed from github, signaling an immediate legal and remediation effort. The company’s action underscores a hard truth noted by industry observers: once implementation code and configuration details are placed on the public internet, containment becomes significantly more difficult. Even with takedowns, copies can persist, and the presence of code fragments or prompting recipes can accelerate adversarial exploration. In practical terms, the move to request removals on github is a first step, but it does not erase the pathways that leaked material can create.
The permanence concern is particularly acute because the leak included operational insights—how to induce specific behaviors in deployed models. That combination of structural code and procedural cues can lower the barrier for reverse-engineering or adapting attack vectors against similar systems. Companies now face trade-offs between transparency and risk mitigation when open platforms like github become the battleground for intellectual property control and security response.
Supply-chain breach at Mercor and cascading risks
The supply-chain incident traced back to an open-source component tied to model training work. A named hacking group claimed it gained access to the affected firm’s customer records. The firm’s role—aggregating expertise across domains to train related AI models—meant its customers included multiple prominent labs. Industry leaders have argued that exposure of consolidated training assets and client relationships can represent not just commercial loss but a strategic intelligence risk, widening the surface available to rival actors who might repurpose stolen data or model artifacts.
Expert perspectives and contested assumptions
Garry Tan, president and CEO of Y Combinator, warned that the combined exposures place an “incredible amount of [state-of-the-art] training data” from “every major lab” online, valuing that material at billions and suggesting it could be accessible to foreign competitors. That view frames the incidents not only as corporate mishaps but as a potential national-security concern.
Marc Andreessen, co-founder of Andreessen Horowitz, characterized the twin episodes as evidence that the industry’s prior posture of “we’ll lock it up” has reached an endpoint, implying a structural shift in how companies must think about operational security and openness. Those assessments highlight a tension: rebuilding trust will require technical fixes, legal interventions such as takedowns on platforms like github, and revised operational practices around code handling and supply-chain vetting.
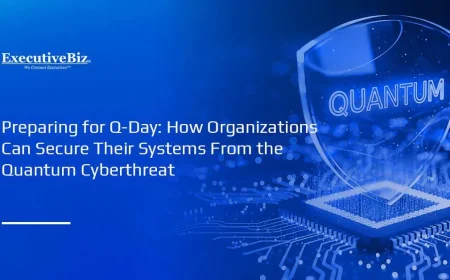
Regional and global implications
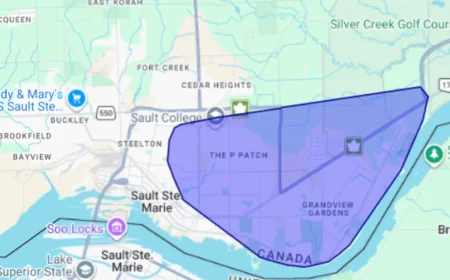
Because the affected training provider works across multiple labs and the leaked code contains prompting and behavior-guidance elements, the repercussions are not confined to a single vendor. The exposures raise cross-border risk considerations: actors with different motives and capabilities could reuse stolen materials to accelerate their own model development or craft targeted attacks. The industry is likely to reassess dependencies on third-party training services and open-source components, weighing speed and collaboration against security and provenance assurance.
Both incidents also sharpen policy conversations about mechanisms for rapid removal, the limits of takedown notices, and the international dimensions of code and data governance. Firms may push for stronger contractual controls with suppliers and expanded monitoring of code-sharing platforms, even while acknowledging that full containment is often impossible.
As companies work to pull leaked assets down from public repositories and shore up supply chains, the AI community faces an open question: can practical, enforceable norms be built that preserve collaborative progress while preventing recurring, high-impact exposures on platforms like github?